Terrorism & Bomb Threats
How quickly your company can get back to business after a terrorist attack, a tornado, a fire, or a flood often depends on emergency planning done today. While the Department of Homeland Security is working hard to prevent terrorist attacks, the lessons of the 1993 World Trade Center bombing, the 1995 Oklahoma City bombing and the September 11, 2001 terrorist attacks demonstrate the importance of being prepared.
Terrorism is the use of force or violence against persons or property in violation of the criminal laws of the United States for purposes of intimidation, coercion, or ransom.
High-risk targets for acts of terrorism include military and civilian government facilities, international airports, large cities, and high-profile landmarks. Terrorists might also target large public gatherings, water and food supplies, utilities, and corporate centers. Further, terrorists are capable of spreading fear by sending explosives or chemical and biological agents through the mail..
Business continuity and crisis management can be complex issues depending on the particular industry, size and scope of your business. However, putting a plan in motion will improve the likelihood that your company will survive and recover. The following information is a good start for small- to mid-sized businesses. Companies that already have their emergency plans in place can continue to help create a more robust sustainable community by mentoring businesses in their own supply chain and others needing advice.
Homeland Security Advisory System
The Homeland Security Advisory System was designed to provide a national framework and comprehensive means to disseminate information regarding the risk of terrorist acts to the following:
• Federal, state, and local authorities
• The private sector
• The American people
This system provides warnings in the form of a set of graduated “threat conditions” that increase as the risk of the threat increases. Risk includes both the probability of an attack occurring and its potential gravity. Threat conditions may be assigned for the entire nation, or they may be set for a particular geographic area or industrial sector. At each threat condition, government entities and the private sector, including businesses and schools, would implement a corresponding set of “protective measures” to further reduce vulnerability or increase response capability during a period of heightened alert.
There are five threat conditions, each identified by a description and corresponding color. Assigned threat conditions will be reviewed at regular intervals to determine whether adjustments are warranted.
Official definitions determine counter-terrorism policy, and are often developed to serve it. Most government definitions outline the following key criteria: target, objective, motive, perpetrator, and legitimacy or legality of the act. Terrorism is also often recognizable by a following statement from the perpetrators.
Violence – According to Walter Laqueur of the Center for Strategic and International Studies, "the only general characteristic of terrorism generally agreed upon is that terrorism involves violence and the threat of violence". However, the criterion of violence alone does not produce a useful definition, as it includes many acts not usually considered terrorism: war, riot, organized crime, or even a simple assault. Property destruction that does not endanger life is not usually considered a violent crime, but some have described property destruction by the Earth Liberation Front and Animal Liberation Front as violence and terrorism; see eco-terrorism.
Psychological impact and fear – The attack was carried out in such a way as to maximize the severity and length of the psychological impact. Each act of terrorism is a “performance” devised to have an impact on many large audiences. Terrorists also attack national symbols, to show power and to attempt to shake the foundation of the country or society they are opposed to. This may negatively affect a government, while increasing the prestige of the given terrorist organization and/or ideology behind a terrorist act.
Perpetrated for a political goal – Something many acts of terrorism have in common is a political purpose. Terrorism is a political tactic, like letter-writing or protesting, which is used by activists when they believe that no other means will effect the kind of change they desire. The change is desired so badly that failure to achieve change is seen as a worse outcome than the deaths of civilians. This is often where the inter-relationship between terrorism and religion occurs. When a political struggle is integrated into the framework of a religious or "cosmic" struggle, such as over the control of an ancestral homeland or holy site such as Israel and Jerusalem, failing in the political goal (nationalism) becomes equated with spiritual failure, which, for the highly committed, is worse than their own death or the deaths of innocent civilians.
"Terrorism is defined as political violence in an asymmetrical conflict that is designed to induce terror and psychic fear (sometimes indiscriminate) through the violent victimization and destruction of noncombatant targets (sometimes iconic symbols). Such acts are meant to send a message from an illicit clandestine organization. The purpose of terrorism is to exploit the media in order to achieve maximum attainable publicity as an amplifying force multiplier in order to influence the targeted audience in order to reach short- and midterm political goals and/or desired long-term end states."
Deliberate targeting of non-combatants – It is commonly held that the distinctive nature of terrorism lies in its intentional and specific selection of civilians as direct targets. Specifically, the criminal intent is shown when babies, children, mothers and the elderly are murdered, or injured and put in harm's way. Much of the time, the victims of terrorism are targeted not because they are threats, but because they are specific "symbols, tools, animals or corrupt beings" that tie into a specific view of the world that the terrorists possess. Their suffering accomplishes the terrorists' goals of instilling fear, getting their message out to an audience or otherwise satisfying the demands of their often radical religious and political agendas.
Disguise – Terrorists almost invariably pretend to be non-combatants, hide among such non-combatants, fight from vantage points in the midst of non-combatants, and (when they can), strive to mislead and provoke the government soldiers into attacking other people, so that the government will be blamed. When an enemy is identifiable as a combatant, the word "terrorism" is rarely used.
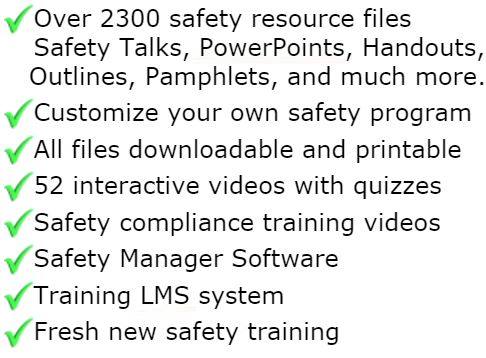
All materials in the members area for this topic index

GET INSTANT ACCESS
to THE MEMBERS LIBRARY
Safety materials created by safety professionals.
Access to the Safety Manager software.
Wide variety of safety videos and courses.
**Brand New** Safety Training Management System
Pre-Made Safety Materials Ready For Use
Created by experienced safety professionals & risk consultants. Saving you time, money, and risk of injuries.
95% of the work already done.
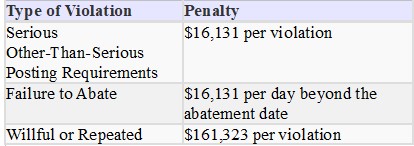
Below are the maximum penalty amounts, with the annual adjustment for inflation, that may be assessed after Jan. 15, 2024. (See OSHA Memo, Jan. 8, 2024).
**New OSHA HEAT 90 DAY**
>>Download Free HERE<<
**New 2024 OSHA 300 Form**
>>Download Free HERE<<
**Brand New**
Free with full membership subscription
Training LMS System
Ask The Safety Consultant
Safety Equipment Deal Finder
“SafetyInfo.com is the first go-to website for safety professionals and companies to use in establishing a solid safety program"
-Mike McKenzie, Certified Safety & Health Manager (CSHM), McSafety Solutions™
Note: You must have a full subscription to the Safety Library in order to use this material. Any use outside of your organization, for resell, or without an active membership is strictly prohibited and may result in prosecution under copyright infringement laws. Please contact us first, if you would be interested in reselling or using our materials for reproduction.
Inside the Members Library
Topic Index
Accident Prevention
Air Quality
Asbestos
Bloodborne Pathogens
Boilers
Chemical Safety
Compressed Gas
Confined Space
Construction
Construction Worksite
Cranes & Slings
Driver / Fleet Safety
Drug Free Workplace
Electrical
Emergency Management
Engineering Safety
Environmental
Equipment
Ergonomics
Fall Protection
Fire Safety & Prevention
First Aid
Flammable Materials
Forklifts
Hazard Communication
Hazardous Materials
Hearing Protection
Heat Stress
Hot Work
Housekeeping
Job Safety Analysis
Laboratory
Ladders
Lead
Lockout-Tagout
Machinery & Equipment
Material Handling
MSDS (SDS)
Medical & First Aid
Occupational Health
Office Safety
Off the Job Safety
Personal Protection
Process Safety
Record Keeping
Respiratory Protection
Silica Safety
Rules & Policies
Signs & Labels
Slips, Trips & Fall
Training
Terrorism Programs
Tool Safety
Vehicle & Driver
Violence Programs
Welding & Hot Work
Training Videos
Library Index
Training Materials
Videos/Courses
Talks
Articles
PowerPoint
Handouts
Training Overheads
Quizzes
Supervisor Briefs
Management Briefs
Safety Sessions
2 Minute OSHA Safety Talks
Pamphlets
First Aid Training
Supervisor Training
Hazardous Materials
Bomb Threat
Crossword Puzzles
Biological Agents
Forms & Documents
Forms
Checklists
Audit Guides
Inspections Guides
Signs & Labels
Environmental Audit Guides
Recordkeeping - OSHA 300
Sign & Label Maker
Safety Management Resources
Safety Manuals/Written Programs
Ergonomic Programs
Emergency Plans
Process Safety Management
Construction Safety
Occupational Health
Environmental
Topic Sheets
DOT Fleet-Driver
Hazardous Materials
Chemical Safety
Drug Free Workplace
Terrorism Programs
Development Guides
Safety Manager Software
Safety References & Graphics
Technical Safety Information
Posters
Topic & Fact Sheets
Development Information
Job Specific Safety Rules
Terrorism
Calculators
Safety Comic Strips
New Safety Training System
Schedule and train your employees with our materials. Add unlimited amount of employees. Record all progress and issue certificates. For group and individual training sessions.